Network security challenges have become increasingly serious as we evolve from the Internet era to the IoT era.
Not only has the number of organised, premeditated attacks across all networks increased, but the form of cyber attacks has become more and more complex and advanced.
 In this new age of network security, the roles of the intrusion detection systems (IDS) and intrusion prevention systems (IPS) are gaining increasing importance with their continuous development and innovations. After outlining the new requirements for IDS/IPS equipment to maintain network security in the IoT era, this article will introduce how ADLINK’s CSA-7400 high performance, high density and high scalability platform helped NSFOCUS to build next-generation 100G+ grade IDS and IPS that offer safer, more reliable and more stable solutions for carriers.
In this new age of network security, the roles of the intrusion detection systems (IDS) and intrusion prevention systems (IPS) are gaining increasing importance with their continuous development and innovations. After outlining the new requirements for IDS/IPS equipment to maintain network security in the IoT era, this article will introduce how ADLINK’s CSA-7400 high performance, high density and high scalability platform helped NSFOCUS to build next-generation 100G+ grade IDS and IPS that offer safer, more reliable and more stable solutions for carriers.
New requirements and challenges for IDS/IPS
As traditional firewalls find it increasingly difficult to handle the new types of intrusions in the cyber world, today’s network protection requires more sophisticated and diversified capabilities. As a result, IDS/IPS have gradually become indispensable components for building an effective network security system. An IDS monitors network operations security by gathering and analysing information on the entire network in order to instruct the operator of the required adjustments of security rules, while an IPS blocks intrusions by executing security rules in real time after in-depth analysis of network data.
Traditional detection technologies – challenges of protecting web-based networks
To enhance detection rates and minimise error rates, both IDS and IPS are equipped with comprehensive detection technologies including feature matching, protocol analysis and anomaly detection.
Feature matching is by far the most commonly used due to its high accuracy and speed. Maximum efficiency of feature matching is dependent on the accuracy of the overall feature library and the feature matching capacity of the equipment.
By discerning the operating principles of a protocol (usually based on RFC standards), protocol analysis searches for suspicious visit behaviours; to detect overflow and denial of service (DoS) attacks. Effective use of this technology enables a high detection rate and a near-zero error rate. Anomaly detection discovers unexpected abnormal traffic through learning and adjusting the normal traffic criteria of a specific network environment. When the actual traffic statistics exceed the threshold value for a given traffic criterion, an anomaly detection alarm is sent.
Despite their advantages, each technology has its flaws. For example, feature matching requires regular updates of the feature library to avoid omissions. Due to the wide variances in each protocol’s implementation and unavailability of complete details for proprietary protocols, protocol analysis can usually only be realised for common protocols such as HTTP, FTP and SMTP. When threshold values are set improperly, anomaly detection can result in false positives. As the number of web-based networks and advanced persistent threats (APTs) continues to increase, the deployment of IDS/IPS relying on these traditional technologies will be inadequate.
About the NSFOCUS
NSFOCUS is committed to tracking the latest trends in network security vulnerability research around the world, continually extending vulnerability analysis, mining, and engineering technology to enhance the technical standards of IDS/IPS, anti-DDoS, malware, and attached behaviour analysis and detection. Furthermore, NSFOCUS spares no effort to actively engage in the research and development of cloud security and virtualisation security, software as a service (SaaS)-based security services, security measurement, security reputation, and security intelligence.
Over the past two years, NSFOCUS Security Labs has published integrated reports on trends in security threats, next-gensecurity architectures, IPv6 security research, and security for industrial control systems. As of the end of 2017, NSFOCUS has published 96 notices on security vulnerability research and assisted Microsoft, Cisco, and Oracle on the discovery and resolution of over 94 security vulnerability problems, making it an important contributor to the national vulnerability database. The NSFOCUS Vulnerability Database (NSVD) is the leading Chinese vulnerability database in China.
 Application of deep packet inspection technology
Application of deep packet inspection technology
The main difference between an IPS and a traditional firewall is that the former can perform deep packet inspection (DPI) of packet contents. If a hacker launches attacks through the vulnerability in Layers 2-7, an IPS can detect and then block such attacks from the data flow. By contrast, the traditional firewall can only detect the quintuple of a data packet (source IP address, source port, target IP address, target port, and protocol at the transmission layer), without detecting the contents at the application layer or individual bytes, thus overlooking many attacks. As an IPS checks each byte of data traffic, it identifies most mainstream application protocols; based on its protocol recognition framework. Then, through nuanced management of the identified information, it can detect the security vulnerabilities in these applications and take the initiative to prevent web attacks.
Application identification using DPI generally requires equipment with large-scale parallel computing ability to filter and detect tens of thousands of packets per second, as well as being able to perform IP defragmentation, TCP stream aggregation and data flow status tracking.
User-based behavioural analysis
In recent years, the mobile network has become an important infrastructure for enterprises, resulting an increasing number of intranet infiltration incidents via wireless networks. In wireless network deployment, open Wi-Fi hotspots for visitors allowing unauthenticated access to the corporate network has become increasingly popular. In addition, employees working off-site may access the company network from their homes, airports and customer’s premises. While effective, these wireless networks often lack effective management, allowing hackers to easily bypass the company’s firewalls, making wireless networks a stepping stone into the company’s intranet.
As the second security gateway after the firewall, IDS/IPS offers user identity and user access control to effectively resolve broken access control (BAC) problems brought about by the roaming of unauthenticated equipment and employees. With the statistical analysis of employee network visit activities of a company, a normal web visit pattern can be built upon features including user identity, geographical location, operating time, visit contents and visit frequency. The system can accurately detect abnormal behaviour deviating from the normal visit pattern and send alarms (IDS) or block the activity (IPS).
Advanced Persistent Threats
Stealing core data is often the goal of APTs. Web attacks and intrusions launched On corporate users are often premeditated over a long period of time and highly concealed. APT attacks are like a special-forces team equipped with comprehensive and sophisticated weapons that can paralyse the defensive power of the corporate web environment’s traditional firewalls and antivirus programmes.
IDS/IPS bring better probability for successfully dealing with APTs. By performing network traffic visualisation, an IDS will send alarms after detecting traffic anomalies to minimise the losses caused by APTs. Through collaboration with the local threat analysis system and based on the APT sample, behaviour analysis and virtual execution technologies, an IPS can discover advanced malicious codes hidden in the traffic and dynamically adjust its protection strategy to block malicious traffic in real time.
NSFOCUS NIDS/NIPS solutions and hardware platform requirements
To allow customers monitor for, detect, and prevent attacks, NSFOCUS offers its brand new NIDS and NIPS intrusion protection solutions.
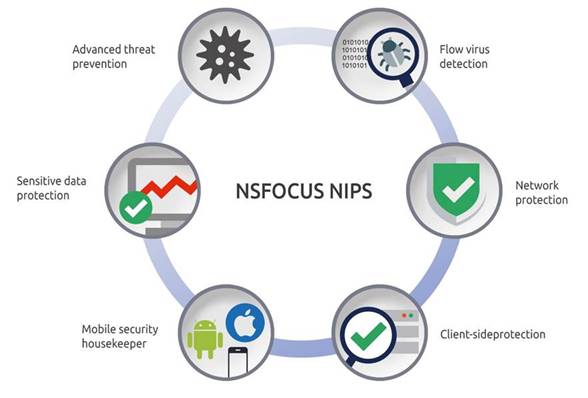
In addition to a having an advanced attack rule feature library for detecting known security threats, NSFOCUS’ NIDS is equipped with a continually updated reputation feature library that can reduce hazards brought by unknown malware and effectively prevent persistent intranet infiltration with its intranet security function, thus minimising leakage of sensitive data and abnormal external connections to servers. NSFOCUS’ NIPS is equipped with a world-leading attack feature library and real-time reputation library. To respond to advanced threats, an integrated sandbox detection capability is used to realise 3D protection for both known and unknown threats. The use of flow virus detection technology can capture hotspot viruses to maximally enhance antivirus capacity. The integrated mobile phone housekeeper realizes a secure enquiry push and secure status real-time monitoring to reduce the workload of maintenance and operation staff.
 Advanced threat prevention NSFOCUS NIPS
Advanced threat prevention NSFOCUS NIPS
Mobile security
To support the security characteristics and requirements of next-generation 100G+ grade NIDS/NIPS platforms, NSFOCUS proposes the following computing platform requirements:
High throughput capacity and I/O density
To better meet the demands of high-end application scenarios of operators such as core networks, cloud computing centres, large enterprises and IDC outlets, NSFOCUS requests support of the 100GB interface on computing platforms for its IDS/IPS products, with each piece of equipment supporting a minimum of 800G traffic connection and of a minimum of 64x 10GB ports. The network ports must support upstream and downstream port consistency and RSS.
Parallel computing and computing density
To support deep packet inspection and other detection methods, NSFOCUS requests that NIDS/NIPS computer platforms support parallel processing capability. In particular, network packet processing platforms should be equipped with wire speed transceiving capability, have the maximum possible computing density per rack unit, and have a zero packet loss rate for small packets of 64 bytes.
Load balancing, same source and same host
In NSFOCUS’ NIDS/NIPS, all data traffic is connected by means of a switch board which balances the traffic load to individual processor boards. When processor board errors are detected, the switch board can redirect the traffic. To ensure processing of the same conversation at the same CPU node, the switch board must support the same source and the same host to automatically merge the data flow of the same conversation.
Carrier-grade high availability
As a NIPS platform must be incorporated into the traffic path, NSFOCUS requires the modularisation of computing platforms in a carrier-grade industrial design to provide uninterrupted services for users with hot swap capability for faulty components (compute, switch, PSU, fan, and storage).
Support for standardised API support for standardised API management
To reduce low-level development burdens, NSFOCUS requires the support for standardised API management of hardware platforms with a set of standardised APIs for traffic and hardware management of all components on the rack, port and VLAN management, commonly used L2/L3 switch protocol stacks, and remote reboot management.
Product features CSA-7400
As a next-generation high-performance telecommunications COTS DPI and network security platform, the CSA-7400, built on ADLINK’s Open Compute Carrier-grade Edge Reference Architecture (OCCERA), achieves high-speed interconnection of compute nodes with dual-redundant switch nodes to offer front panel I/O up to 800GB. The CSA-7400 supports hot swapping of major chassis components to protect uninterrupted business, making it suitable for the next-generation high-performance IDS/IPS.
Unbeatable cooperation
According to NSFOCUS, ADLINK’s expertise in attack prevention developed over the years, this in-depth collaboration with ADLINK enables both parties to build IDS/IPS products meeting the demands of high-end application scenarios such as core networks for operations, cloud computing, large enterprises, and data centres. The interconnected redundant module design and hot swap support for both computing nodes and switches of the OCCERA-based CSA-7400 platform.
ADLINK offer users uninterrupted delivery service.
NSFOCUS’ NIPS products are equipped with various advanced technologies such as the NSFOCUS global threat intelligence system and NSFOCUS unknown threat detection can demonstrate better protection on the CSA-7400. In the future, NSFOCUS will continue close collaboration with ADLINK for its IDS/IPS products to maximize the effectiveness of the excellent features of NSFOCUS’ NIDS/NIPS products on CSA-7400 platform for the network security market.
The CSA-7400 is a next-generation, high performance, carrier grade COTS network security platform built on the Open Compute Carrier-grade Edge Reference Architecture (OCCERA) by ADLINK, integrating network interfaces, switches, and overall computing capacity.
The open hardware architecture and platform scalability of the CSA-7400 support NSFOCUS’ next-generation 100G+ IDS/IPS solutions, allowing NSFOCUS to launch its high-performance NIDS/NIPS products for the network security market. The CSA-7400’s flexibility and configurability enables cross-business product deployment and easy integration to other high-end network security markets, such as next-generation firewalls, telecommunications, and mobile edge computing.
In addition to hardware features, the API library provided by ADLINK allows security solution providers focus on their core competence, enhance business migration increase product efficiency, and shorten product launch and delivery cycles.

